The basic truths about the world, which Buddhists assume to be true. (later, they completely realize that they are actually true)
1 – The truth of dukkha (suffering, anxiety, dissatisfaction)
2 – The truth of the origin of dukkha
3 – The truth of the cessation of dukkha
4 – The truth of the path leading to the cessation of dukkha
Only human beings can reason these truths are related to the reality. Beings in other worlds might have difficulties in reasoning or even believing the above four as truth.
Read More: http://en.wikipedia.org/wiki/Four_Noble_Truths
The Argument | Interdependent Co-Arising
Buddhist argument is based on and flow from the above basic truths and valid for all rational beings who understand logic in all possible worlds (not just for human beings in the sensual realm).
This argument is valid and any intelligent person, if he can reason logically because he practiced it, will accept the argument as a valid argument.
When this is, that is.
From the arising of this comes the arising of that.
When this isn’t, that isn’t.
From the cessation of this comes the cessation of that.Translator: Thanissaro Bikkhu
The argument about dependent origin may seem unsound to the people who don’t understand or don’t accept the four basic truths.
1 -With Ignorance as condition, Mental Formations arise (With Avidyā as condition, Saṃskāra arises)
2 -With Mental Formations as condition, Consciousness arises (With Saṃskāra as condition, Vijñāna arises)
3 -With Consciousness as condition, Mind and Matter arise (With Vijñāna as condition, Nāmarūpa arises)
4 -With Mind and Matter as condition, Sense Gates arise (With Nāmarūpa as condition, Ṣaḍāyatana arises)
5 -With Sense Gates as condition, Contact arises (With Ṣaḍāyatana as condition, Sparśa arises)
6 -With Contact as condition, Feeling arises (With Sparśa as condition, Vedanā arises)
7 -With Feeling as condition, Craving arises (With Vedanā as condition, Tṛṣṇā arises)
8 -With Craving as condition, Clinging arises (With Tṛṣṇā as condition, Upādāna arises)
9 -With Clinging as condition, Becoming arises (With Upādāna as condition, Bhava arises)
10 -With Becoming as a condition, Birth arises (With Bhava as condition, Jāti arises)
11 -With Birth as condition, Aging and Dying arise (With Jāti as condition, Jarāmaraṇa arises)
Read More: http://en.wikipedia.org/wiki/Prat%C4%ABtyasamutp%C4%81da
The Destination | Nibbana
The final destination where Noble Eightfold Path will lead you to. Spiritually, the perfect state of being. I always try to visualize the peace and tranquility I will experience after reaching this state.
Read More: http://en.wikipedia.org/wiki/Nirvana

The Path | Noble EightFold Path
The path taught by the greatest pragmatic teacher. The Perfect Path.
Wisdom
1 – Right view
2 – Right intention
Ethical conduct
3 – Right speech
4 – Right action
5 – Right livelihood
Concentration
6 – Right effort
7 – Right mindfulness
8 – Right concentration
Read More: http://en.wikipedia.org/wiki/Noble_Eightfold_Path

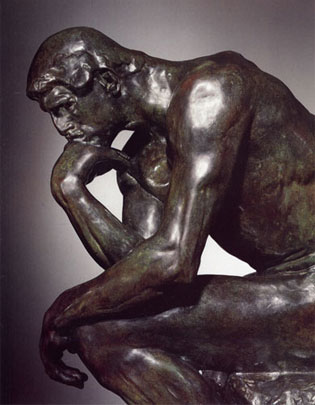
The Thinker: http://en.wikipedia.org/wiki/The_Thinker
Appendix A | Contemporary Ethical Philosophy
Derek Parfit is a moral philosopher, who once described an state of mind where it is nealy close that of a practising Buddhist.
“My life seemed like a glass tunnel, through which I was moving faster every
year, and at the end of which there was darkness… [However] When I changed my view, the walls of my glass tunnel disappeared. I now live in the open air.
There is still a difference between my life and the lives of other people. But
the difference is less. Other people are closer. I am less concerned about the
rest of my own life, and more concerned about the lives of others.”- Derek Parfit
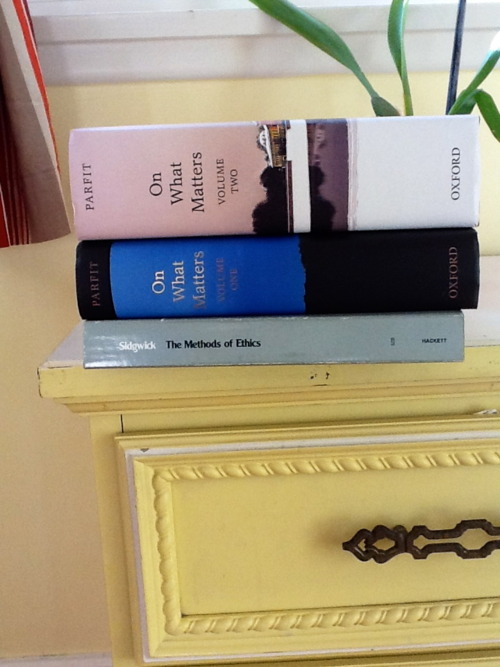
Derek Parfits ‘Reasons and Persons’ (described by Alan Ryan as “something close to a work of genius”) was published in 1984. His second major work(‘On What Matters’) is also available on Amazon. I added both these books to my wish list, wishing to read someday. (I give priority to other books in my wish list. They must be read first.)
See More: http://onwhatmatters.tumblr.com/
Appendix B | Money
Science is science. Politics is politics. Art is art. Economics is economics. Sport is sport. Psychology is psychology. Medicine is medicine. Engineering is engineering. Marketing is marketing. Business is business. Technology is technology.
Buddhism is Buddhism. Buddhism is necessary, but not sufficient.
When you are hungry, you can’t eat ethics. So make sure you make enough money to buy foods and maintain your moral standards.
(Currently, the distribution is NOT according to the moral value. Needs more reading on Economics?)

]]>“We are the animals that can both understand and respond to reasons. These abilities have given us great knowledge, and power to control the future of life on Earth. Though there may be life elsewhere, there may be no other animals like us. We may be the only rational beings in the Universe.”
– Derek Parfit
– On What Matters Volume One (June 20, 2011)
+ Part One: Reasons
+ Chapter One: Normative Concepts
+ Section One: Sufficient and Decisive Reasons
+ Page: 60
+ The above is the opening sentence of the first paragraph.





 Jesus and the doctors of the Faith, a painting by a follower of Giuseppe Ribera.
Jesus and the doctors of the Faith, a painting by a follower of Giuseppe Ribera.